MISC
Quote from “Principles of Computer System Design: An Introduction”:
For both confidentiality and authentication, Alice first encrypts and then signs the encrypted message (i.e., SIGN(ENCRYPT(M , K_encrypt ), K_sign )), or, the other way around. (If good implementations of SIGN and VERIFY are used, it doesn’t matter for correctness in which order the operations are applied.)
A recent paper on the topic on the order of authentication and encrypting suggests that first encrypting and then computing an authentication tag may cover up certain weaknesses in some implementations of the encrypting primitives. Also, cryptographic transformations have been proposed that perform the transformation for encrypting and computing an authentication tag in a single pass over the message, saving time compared to first encrypting and then computing an authentication tag.
Resources
RFCs
- RFC7468 Textual Encodings of PKIX, PKCS, and CMS Structures
- RFC5280 Internet X.509 Public Key Infrastructure Certificate and Certificate Revocation List (CRL) Profile
- RFC8017 PKCS #1: RSA Cryptography Specifications Version 2.2
- RFC5208 Public-Key Cryptography Standards (PKCS) #8: Private-Key Information Syntax Specification Version 1.2
- RFC5958 Asymmetric Key Packages
MISC
- Chain of trust
- What is the SSL Certificate Chain?
- Root certificate
- Certificate Binary Posters (Part One)
- Certificate Binary Posters (Part Two)
- ASN.1 syntax
- DER encoding
- A Layman’s Guide to a Subset of ASN.1, BER, and DER
- How to find modulus from a RSA public key?
- Is there a specification for the “BEGIN RSA PRIVATE KEY” format?
- How to generate PKCS#1 RSA keys in PEM Format?
- Why RSA private key is larger?
- What are the differences between .pem, .cer and .der?
- Is there a specification for the “BEGIN RSA PRIVATE KEY” format?
- DER Encoding of ASN.1 Types
- OpenSSL 1.0.2 man pages
- How Apple dodged the Heartbleed bullet
- Why is Apple Deprecating OpenSSL in MacOS 10.7 (Lion)?
- The TLS mess in OS X El Capitan
- RSA: Get exponent and modulus given a public key
- Public key cryptography - Diffie-Hellman Key Exchange
- CLIENT-SIDE CERTIFICATE AUTHENTICATION WITH NGINX
- Check your SSL/TLS certificate installation
- SSL Server Test
- How to view all ssl certificates in a bundle?
- How does SSL/TLS work?
OpenSSL
pkcs8 - PKCS#8 format private key conversion tool
cat ca.key | openssl pkcs8 -topk8 -nocrypt
openssl genrsa -out my-safe-directory/1024.key 1024
openssl req uses -config to specify configuration file.
openssl x509 uses -extfile to add extentions.
Client-side Certificate Authentication with Nginx
Generate keys and certificates follow instructions in CLIENT-SIDE CERTIFICATE AUTHENTICATION WITH NGINX. Ngnix configuration:
ssl_client_certificate /home/jing/complete/ca.crt;
ssl_verify_client on;
Allow access to imported privateKey:
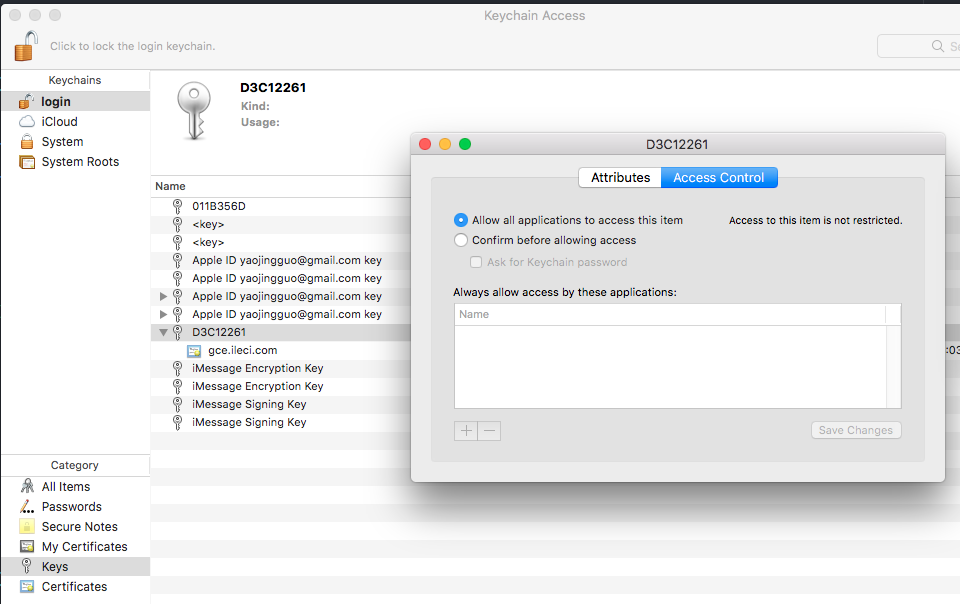
http https://gce.ileci.com --cert user.crt --cert-key user.key works. When
Enter PEM pass phrase: appears, import password for private key.
X509 Extension
- Add extensions with
openssl req: https://security.stackexchange.com/a/91556/183595 - Add extensions with
openssl x509: https://security.stackexchange.com/a/159537/183595
openssl x509 -req will only honor extension in x509 own configuration. It will
omit extensions contained in the CSR.